#security (2019-08)
Archive: https://archive.sweetops.com/security/
2019-08-02

The recent disclosure of yet another cloud security misconfiguration leading to the loss of sensitive personal information made the…
2019-08-05
Anyone here have any experience with network micro segmentation on AWS? Just starting down the path of researching this subject and looking for links/recommended tools esp./papers
can you elaborate on your usecase?
Where I’m at right now, I spend a lot of time trying support network comms and the things allowed to egress/ingress on each subnet with a combination of Network ACLs, Security Group rules and outbound Palo Alto Networks firewalls.
This is the customer’s design and I can already see it starting to reach it’s limits. On AWS NACLs you get 40 ingress and 40 egress rules per subnet at max…
I saw some interesting articles about network “microsegmentation” a few years ago, but never had a chance to look at it. I think this is what the customer is trying to achieve - complete control and visibility of an Apps traffic flows across the network with a “whitelist” only approach down to ports + protocols.
I’ve had to table this topic for at least on more sprint, but will probably do a spike on it in soon.
2019-08-08
Anyone tried https://github.com/bitnami-labs/sealed-secrets
A Kubernetes controller and tool for one-way encrypted Secrets - bitnami-labs/sealed-secrets
We use it. Simple and reliable. Have added some Prometheus metrics And mixin in a fork. Waiting for maintainer feedback before submitting PR.
A Kubernetes controller and tool for one-way encrypted Secrets - bitnami-labs/sealed-secrets

Changes to configuration files don’t change signature, can add malicious features.
2019-08-09

One in four firms holding a test subject’s data released it to her partner without her permission.
@Erik Osterman (Cloud Posse) going to use this one in my industry updates for my meetup. its a great article

One in four firms holding a test subject’s data released it to her partner without her permission.
This is serious and confirms my suspicions with this well-intentioned but wholly unrealistic provision of GDPR.
This should be a walk in the park for identity thieves. Thieves are already able to social engineer their way through companies with that make it difficult for identify thieves (banks, telephone companies, etc). How are smaller, less sophisticated companies going to be capable of perform sufficient identity verification?
2019-08-14
2019-08-27
Has anybody used any of the AWS WAF subscriptions? Any feedback?
From reviews, looks like it’s really a black box
I have used them
what do you want to know?
They’re totally a black box
you can setup some logging now to see what gets blocked, but you have no influence on changing that blocking rule
For compliance reasons, you can setup a “swiss cheese” WAF….and maybe for some protections on some wordpress or static sites.
I can’t recommend them else where, but that was my experience with it about 1.25 years ago. If you can afford it, I hear great things about Signal Sciences.
@Jonathan Le “ no influence on changing that blocking rule” sounds like a non-starter.
Or is there an ability to whitelist/bypass the rules?
It was a large glob of rules when I was using it - not sure if they broke that out in the last year. If they did, I’d imagine that for each exposed rule name you can do “Override to count”, which basically makes that specific rule fire with a “[non]fail to open”.
If you investigate it, let me know if they expose the rules now.
2019-08-28
Did anyone Come across NPM memory Issues ?
2019-08-29
On May 31th, the Kubernetes Product Security Committee announced a security regression in Kubernetes for which they had assigned CVE-2019-11245. The problem caused containers that use images which are supposed to run with a non root user to run as root, on the second time they are used or upon restart of the container. Before …
2019-08-30
Hey, anyone using Pomerium?
I wouldn’t trust any 3rd party proxy/vpn provider to allow access to my internal infrastructure, regardless of the purpose of such infrastructure.
What do you use?
openvpn if I need a vpn
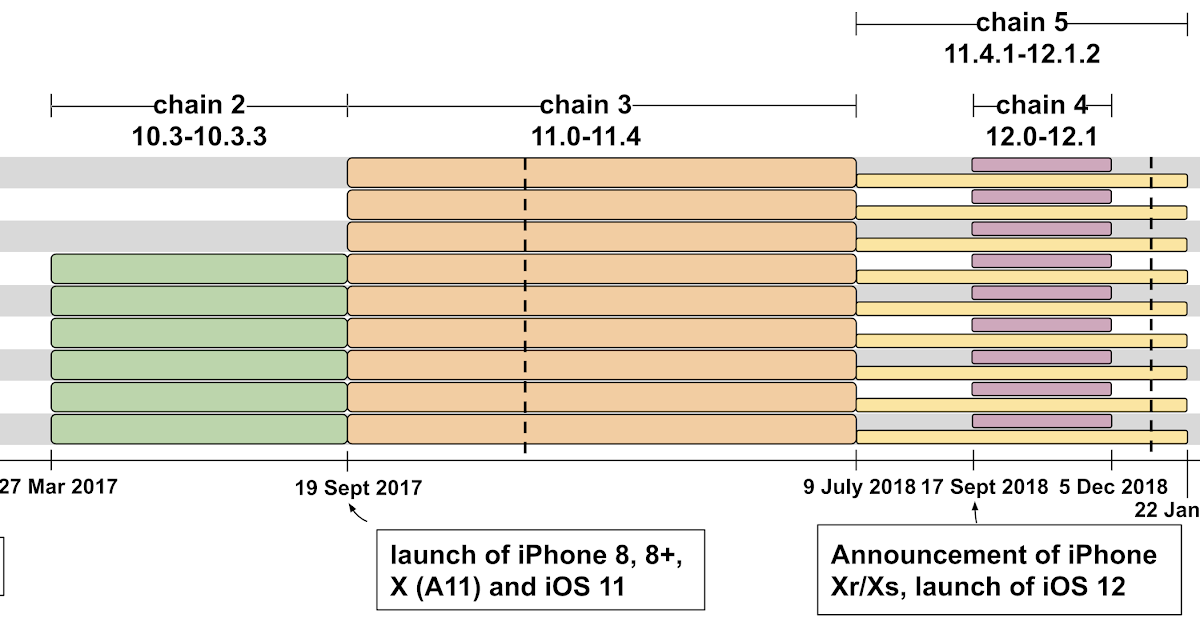
Posted by Ian Beer, Project Zero Project Zero’s mission is to make 0-day hard. We often work with other companies to find and report se…
