#security (2019-09)
Archive: https://archive.sweetops.com/security/
2019-09-02
2019-09-04
is there more of a security risk having SHA1 (i.e. AES128-SHA, ECDHE-ECDSA-AES128-SHA) ciphers in the ELB TLS security policies?
as always, it depends
here’s more on the subject. https://wiki.mozilla.org/Security/Server_Side_TLS
thanks!
2019-09-05
grsecurity is an extensive security enhancement to the Linux kernel that defends against a wide range of security threats through intelligent access control, memory corruption-based exploit prevention, and a host of other system hardening that generally require no configuration.
2019-09-06
2019-09-07
Looking at a dataset of 350 million ssl connections inspires some initial questions:
2019-09-10
Anyone have experience with running Palo Alto networks firewalls at scale on AWS?
2019-09-12
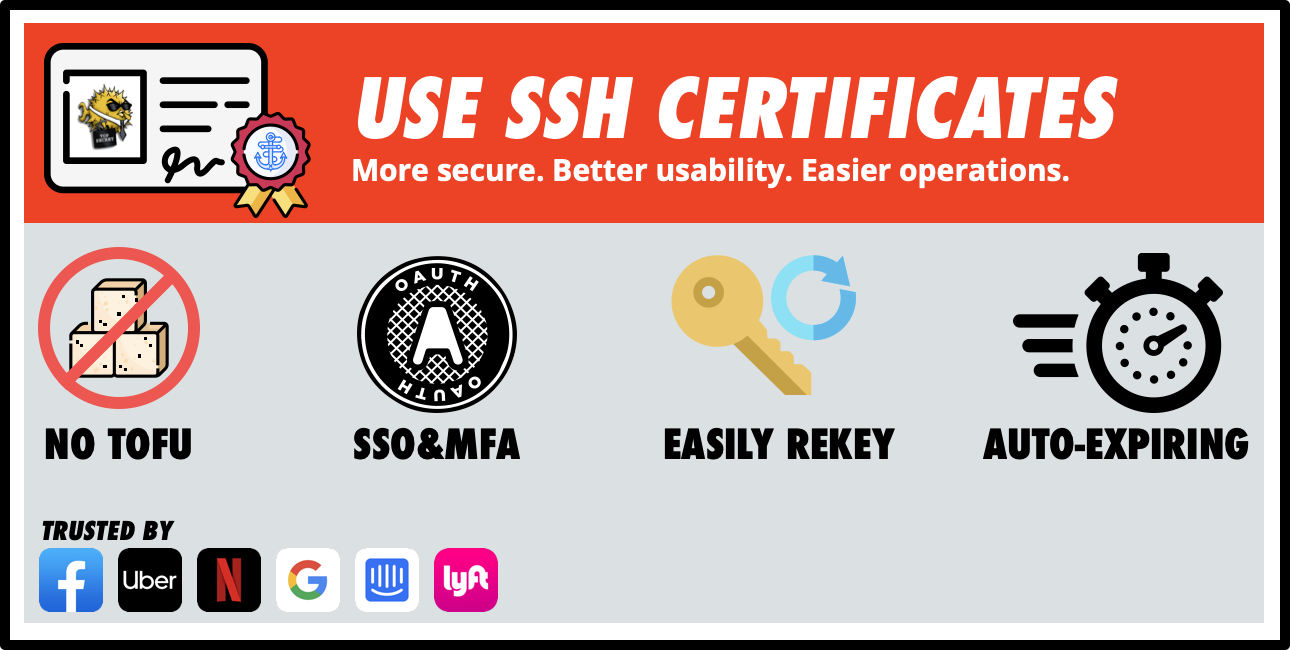
SSH has some pretty gnarly issues when it comes to usability, operability, and security. The good news is this is all easy to fix. SSH is ubiquitous. It’s the de-facto solution for remote administration of *nix systems. SSH certificate authentication makes SSH easier to use, easier to operate, and more secure.
How does this compare to teleport by gravitational? Looks very similar.
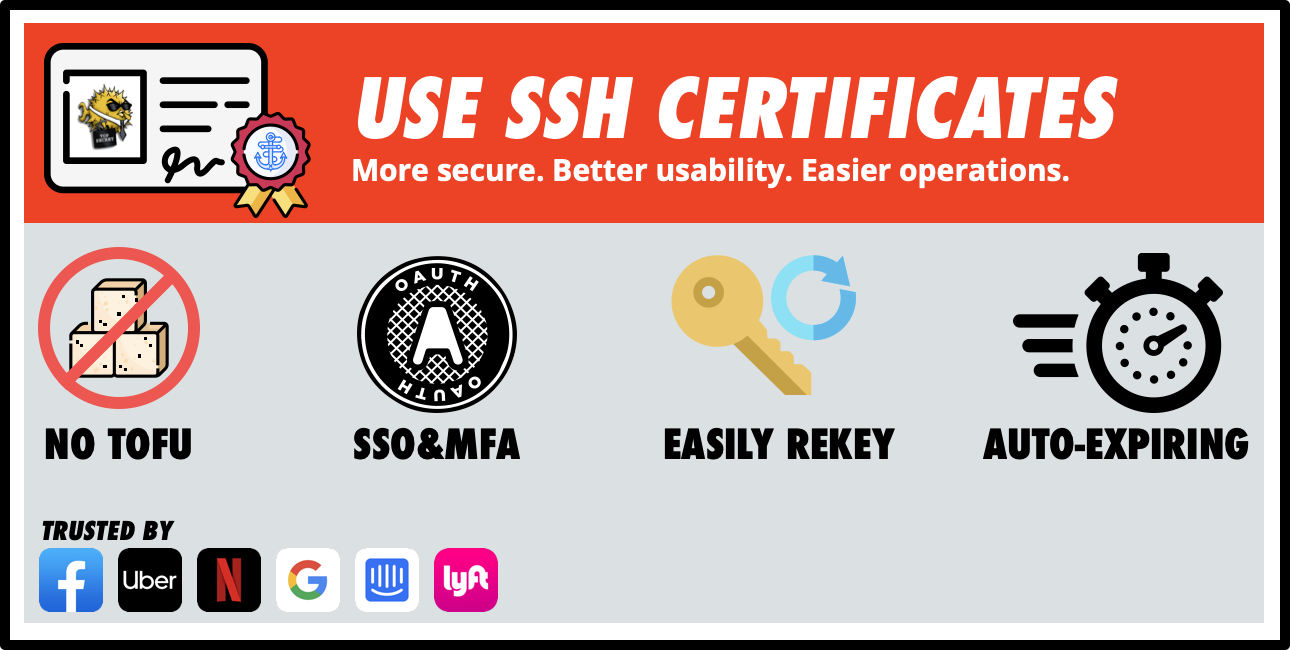
SSH has some pretty gnarly issues when it comes to usability, operability, and security. The good news is this is all easy to fix. SSH is ubiquitous. It’s the de-facto solution for remote administration of *nix systems. SSH certificate authentication makes SSH easier to use, easier to operate, and more secure.
Yep. This is what teleport does (and then some!)
teleport adds full TTY session logging and replay which is priceless. no other solution has that.
@kskewes do you use teleport?
This article goes more into the theory of why you should do it and how you would do it with off the shelf open source software.
Thanks for quick reply. I only skimmed the article but it looks good whichever way one goes. I’ve been wanting to roll out teleport for a year but other projects keep leap frogging it. So not yet… :(
Are you on k8s?
Mostly. We have some bare metal with GPU that we will move to VM soon. We’re about to embark on migration to AWS from IBM.
2019-09-16

Google Project Zero security researcher reveals that the LastPass password manager could, somewhat ironically, leak the last password you used to any website you visited
Thanks for sharing, Erik